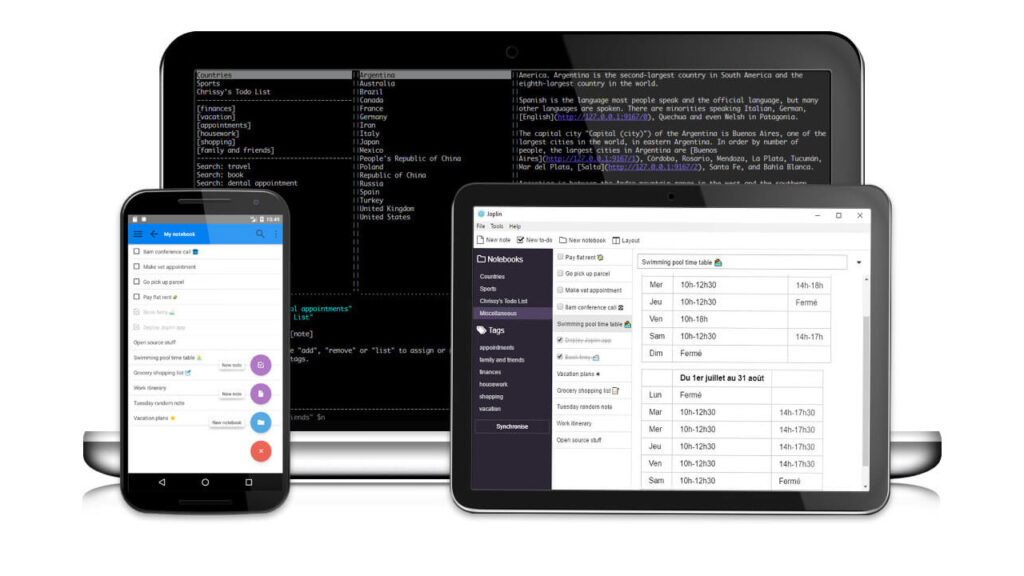
How to use Free Opensource Joplin App Note taking
As the Time changes Preference is also change for Note Taking Solution Now Joplin App a Note Taking Application Respect Privacy, Windows, Linux MacOs and Android or IOS even Command-Line VIM, When I started Note Taking that time Only Has windows Environment and One Note was Bundled with Office and Synchronization with Multiple computer Home […]
How to use Free Opensource Joplin App Note taking Read More »